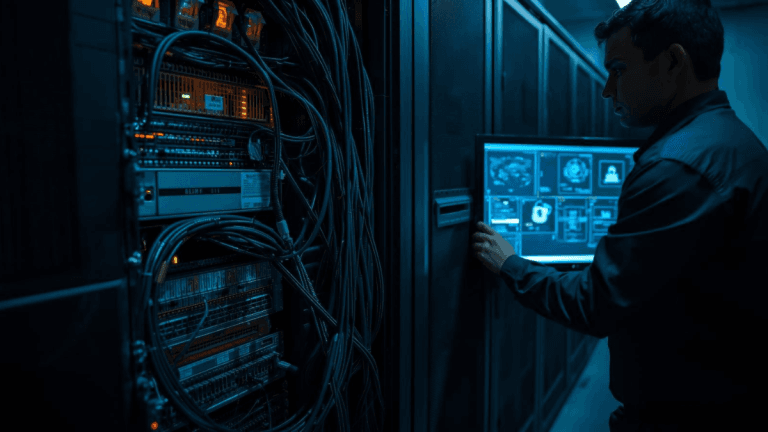
A critical Windows kernel zero-day highlights the importance of fast patching to secure the system’s core.
When Microsoft revealed that a Microsoft Windows kernel zero-day was being attacked, it was more than a headline about hackers. This vulnerability put the spotlight on the very foundation of digital life.
A Microsoft Windows kernel zero-day means bad actors got ahead, reaching into the core of computers that power everything from homes to global industries. The Microsoft Windows kernel zero-day patch was not just a routine security check but a necessary act for the safety of millions of users.
What is the Microsoft Windows kernel zero-day?
Imagine the kernel as the central operating room in every Windows computer. It manages hardware, memory, and every critical function needed to run modern software.
When a gap appears in this layer, it is as if someone can sneak past every locked door in a building. The Microsoft Windows kernel zero-day describes a problem found and exploited before security teams learned it even existed.
Attackers managed to use the flaw to elevate their access, controlling systems in ways that typical antivirus tools often miss.
The path of exploitation
Attackers did not wait for Microsoft to discover the issue. The Microsoft Windows kernel zero-day was used in real campaigns, often as part of multi-phase attacks that rely on small individual weaknesses stacked together.
This exploitation allowed intruders to move from minimal user rights to deep system control. By chaining the Microsoft Windows kernel zero-day flaw with other tricks, they outmaneuvered many standard protections.
Why does it matter right now?
The Microsoft Windows kernel zero-day is important to every sector. Windows is everywhere; in hospitals, banks, schools, and government offices.
The reach means a vulnerability at the kernel level is never isolated. Updating quickly after the release of the Microsoft Windows kernel zero-day patch is critical to block widespread attacks.
The message for every organization and home user is clear: when a Microsoft Windows kernel zero-day is announced, delaying the update can increase risk throughout an entire network.
Lessons beyond the patch
The story of the Microsoft Windows kernel zero-day reminds everyone that security is always unfinished. Even as companies use better tools and smarter AI to scan their code, new flaws still appear.
The cycle is familiar. Researchers and engineers race to prevent gaps before criminals find them, yet sometimes the attackers win the sprint.
For users, layered defenses, quick patching, and paying attention to alert notifications are more than good habits. These steps help to shrink the time window where an exploit is dangerous.
Who is affected most?
The Microsoft Windows kernel zero-day matters to more than just IT professionals. Large companies risk financial losses and legal issues. Hospitals risk patient data and care. Smaller businesses often lack dedicated security, making them easier targets.
Even average people could face malware infections that spread using the Microsoft Windows kernel zero-day as a launch point for deeper attacks.
Looking ahead
After every Microsoft Windows kernel zero-day patch, attackers often look for ways to modify or replicate the exploit. History shows that threats can spike after public disclosure, as more malicious actors work to take advantage before everyone updates.
Security experts treat these moments as reminders to strengthen monitoring, share information quickly, and encourage immediate action across entire digital ecosystems.
The takeaway
The Microsoft Windows kernel zero-day patch shows the importance of routine security updates and paying attention to news from trusted sources. Behind every headline, there are real efforts to keep systems safe so that the technology supporting daily life can be trusted.
By responding quickly and building habits around regular updates, businesses and individuals both help close the door on the risks revealed by the Microsoft Windows kernel zero-day experience.